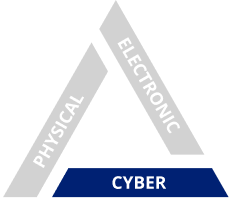
Dedicated to Keeping Organizations Safe Through Our Integrated Security Model
At TriCorps, we operate using our integrated security model to ensure our clients’ safety as threats evolve and technology advances.
Integrated security is the only real security; anything else will fail. Physical, electronic, and cybersecurity must work together and evolve faster than the threats. An active shooter, a cyber-attack, or theft of your property or data could be catastrophic for your organization.
TriCorps is the only integrated security firm with the experience and technology to protect your organization from these dynamic threats.

A disgruntled employee was recently terminated and has returned to the office building to confront their former boss. They are spotted on surveillance cameras and authorities are called, but without a physical security presence, several employees are assaulted before police arrive.

A vendor for a corporate office building is screened upon entry for weapons and is cleared. Without access control at critical doors, the vendor gained entry to the CEO’s office and left with some of the company’s proprietary information.

An employee enters their office building with their access control badge and raises no flags with the security officers during a routine security screening of their bag. They sit down at their desk to check their email and click a link from an unknown sender that exposes the organization’s entire server to ransomware.

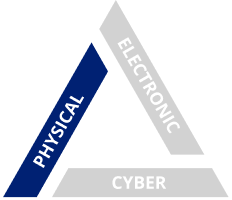
Physical Security
Since 2000, we have provided physical security tailored to ensuring the protection of our clients and their assets. Our physical security experience ranges from deploying officers onto various corporate and field sites, protecting executives, dignitaries and VIPs, and use of our rovers across the country. Our armed and unarmed officers are the backbone of our company.
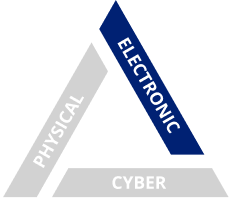
Electronic Security
TriCorps has developed a robust electronic security program to stop crime in its tracks. TriCorps provides turn-key commercial and residential security solutions to meet our client’s needs, including high-definition cameras, access control systems, intrusion detection systems, and GPS trackers.

Cybersecurity
In order to help organizations defend themselves from a growing amount of cyber threats, we have blended the talents of our law enforcement and technology experts to provide organizations with cybersecurity solutions that are unmatched in the industry.